Our Client’s Cryptolocker Story – Part One
Cryptolocker Attacks Our Client’s Files
This past weekend one of our clients mistakenly clicked on an attachment in an email that appeared to legitimately come from FedEx International. The PDF attachment was a shipping label or so it said. Up-to-date A/V scanned it as it was opening, but nothing actually opened! The PDF was a silent script that sent malware out into the computer, encrypting all PDFs, all Office docs, pictures, music files, text files, etc. Once done on the local computer, it went to ALL mapped drives the workstation was using to connect to the server. EVERY folder where the logged in user had write access provided, the malware encrypted every user-created file in those directories as well. We estimated that over 30,000 files were affected.
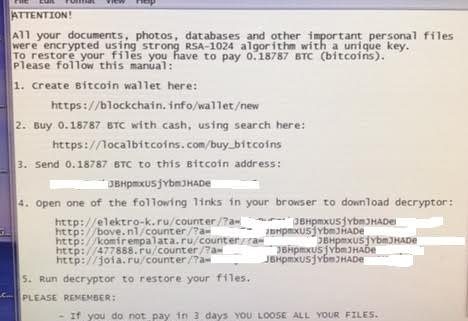
Ransom Demanded
As soon as it was done, a text file pop-up appeared on the computer screen with instructions on how to get a decrypt key. This particular ransomware thief only wanted .18787 bitcoin which translated to $122.11. The process is poorly documented and appears quite shady. And unfortunately, it is very likely the only hope available to get recent data restored. Backups exist but aren’t as up-to-date as they should be.
FBI Discourages Paying Cryptolocker Thieves
Researching bitcoin purchases, we came across a blog where the FBI asks customers to NOT pay the ransom as it encourages further attacks. The article suggests contacting FBI resources to report the attack…something we are going to help the customer do.
Simple Steps to Prevent Cryptolocker or Other Ransomware
How can you prevent or recover from a Ransomware attack? Here are four ways:
- 1) Make regular disconnected backups of your data on workstations and servers. Run the backup to a USB external drive from your workstation and then unplug it. This could be simple drag-copy of your important files to the external storage. Or if you use Carbonite, Mozy, One-Drive or other cloud storage, as soon as you’re done synchronizing, logout.
- 2) Use Malwarebytes with the Ransomware plug-in or contact us to provide a quote for you to use the Sophos Central cloud scanning with their new Intercept-X ransomware killer. I’m not trying to make a sale here, I’m hopefully providing protection solutions for you. Be sure that the anti-virus product you use is up-to-date and that it will at least try to protect against ransomware.
- 3) Convert all regularly used login accounts to Standard User so that a user doesn’t have complete access to the entire computer hard drive or the computer registry. Evaluate/audit who (which log-in accounts) has Write access to network shares/drives. If someone doesn’t need Write access to a server location, take it away.
- 4) Educate all of your users to be wary of anything coming into their email/mailbox, whether it is coming from a sender they are familiar with or not. You don’t know if a familiar sender’s email account has been compromised by a ransomware creator or not. If there is even the slightest hint of a problem…tell your staff to pick up the phone and call the sender to verify before opening. The few minutes they spend making a call, could save your company data.
Ransomware attacks are the most heinous of any malware attacks I’ve seen in more than 25 years in the computer industry. There isn’t any punishment possibly because nearly all attacks originate overseas. The attack mentioned above from this weekend offered five URLs to contact after payment is made…four of the five are from Russia.
Any questions or concerns? Please contact us at skunau@igtg.net.
Please share this blog post with your colleagues to help prevent more malware/ransomware attacks.
In the next entry on this blog topic, we will detail how we were able to solve this ransomware attack.